Home | Business Advice | Business Columnists | Surviving During Uncertain Times
These are challenging times. New information is coming out on a daily basis. There is a good chance that the way you run your business today is not the way you were running it when the new year started. We asked our writers to create articles that help you run your business while maintaining your social distancing.
Recently, Microsoft issued a warning about new phishing scams that try to lure victims with fake COVID-19 news from the Centers for Disease Control (CDC). Phishing is a widely-used scam tactic that disguises emails to appear as if they come from a legitimate source to trick recipients into sharing sensitive information, such as log-on credentials, credit card or bank account information, or Social Security numbers. Phishing is so successful that it is responsible for billions of dollars of business and consumer losses each year.
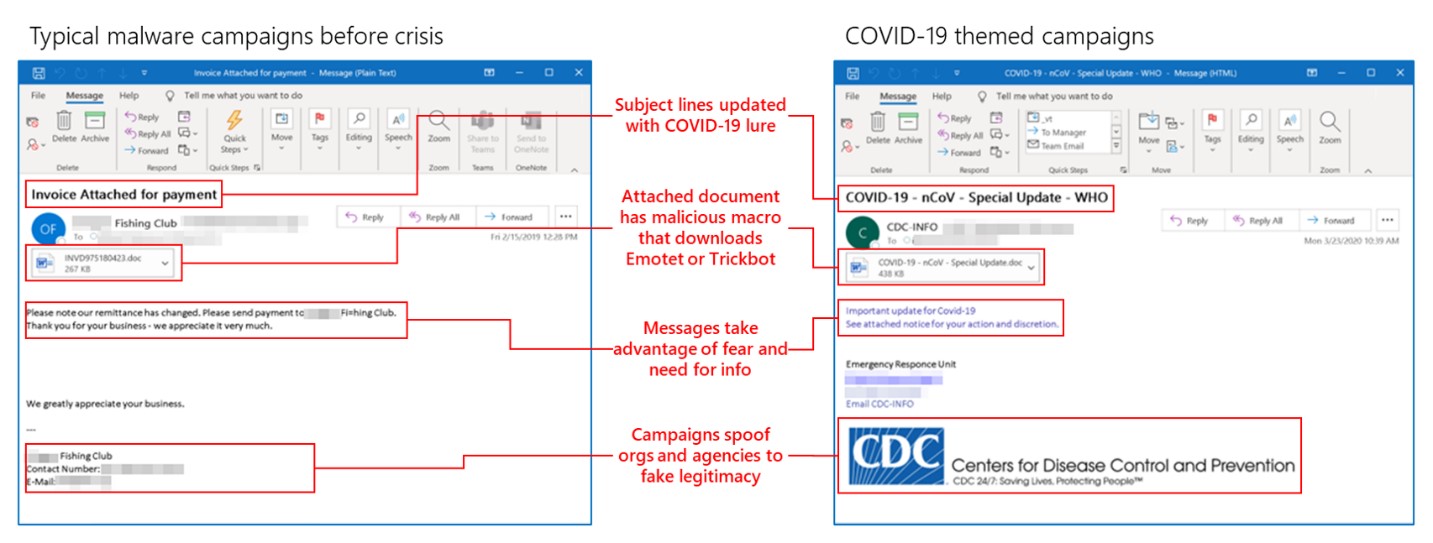
Image via Microsoft
How Phishing Attacks Work
There's a good chance you or a member of your organization has been the target of a phishing attack. Phishing emails arrive in your inbox looking as they were sent from a reputable source, such as your bank, a service company, a government agency, or maybe even someone within your organization. In the email, that might include your name in the salutation, you might find an alert about an account that needs updating or a recent order you placed. The message is designed to get you to click on a link embedded in the email.
If you click on the link, you will be directed to a website that looks legitimate, asking you to enter your login credentials. If you do, the phisher has all it needs to impersonate you on the real website. With some phishing emails, clicking on the link unleashes a virus or malware that can steal your data or encrypt it to hold it for ransom. Worse yet, it also uploads a keylogger component, which can record computer users' keystrokes as they enter passwords and other confidential information.

Image via Shutterstock
COVID-19 Scams Proliferate
The phishing campaign identified by Microsoft delivers a widely-used malware called Lokibot which, in this case, uses COVID-19 as the lure to click on a link. The email pretends to be from the CDC, with subject lines such as Business Continuity Plan Announcement for May 2020. When Lokibot is unleashed, it steals login credentials. Worse yet, it also uploads a keylogger component, which can record computer users' keystrokes as they enter passwords and other confidential information.
While Microsoft was able to detect the attack and update its anti-virus program, Microsoft Defender, to stop it, cybercriminals are working overtime to find new ways to deliver their malware. It's estimated that thousands of different malware attacks disguised as important COVID-19 information are launched each day.
How to Defend Against Phishing Attacks
You and your employees are your first and last line of defense against phishing attacks. To fortify your defenses, you need to educate everyone in your organization on what a phishing attack looks like and how to combat it. Here are six red flags to look for in suspicious emails.
- Fake sender address: An email may look legitimate, but by scrutinizing the sender's address, you can see if there are any misspellings or an extra dash in the address. Sometimes the lower cap letter "L" is replaced with the number "1".
- Generic or "phishy" salutation: If the salutation doesn't contain your name, consider it spam and delete it. Some emails might include an odd form of your name in the salutation, such as your email moniker (i.e. frsmith). If the email doesn't get your name right, delete it.
- Urgent call-to-action: Any email that contains urgent calls to action, such as "your account will be closed" or "action required," should be considered suspect. Look for other red flags and have your supervisor review it.
- Request for sensitive information: Just know that any legitimate business or government agency will never request confidential information. Delete it.
- Phony links: Most phishing scams are all about the links. Never click on a link unless you are 100% certain of the source. Avoid links that don't start with "https" in the URL. If there is no "s", it's probably fake.
There is no better defense against security attacks than becoming thoroughly educated about the risk and arming yourself, your family, and your employees with the knowledge to prevent them. It is also essential to boost your cybersecurity defenses with an upgraded firewall.
